I came across this project on Github that contains source code for achieving undetectable root + loading of arbitrary code on Dell IDRAC7 & IDRAC8 IPMI/BMC server hardware. Although this doesn't work with previous versions of iDRAC that I've written about (v6), the techniques used to adjust the firmware images are applicable.
This work got plenty of attention: ServeTheHome, The Register and AnandTech all wrote about this BMC vulnerability. Dell's own publication of CVE-2018-15774 and CVE-2018-15776 addresses the affected iDRAC releases and specifically mentions that iDRAC systems should not be publicly available.
Duh.
I won't comment further on this issue since it's already covered well enough in the above links. Just thought I'd mention it here briefly in case someone was looking for ways to take control over their own iDRAC systems.
For some time now I've been thinking about the The Web We Lost. I'm certainly not the first person to be commenting on this epoch: Anil Dash has some very cogent points on the matter as have others. The lost web doesn't only refer to the infrastructure or systems that enabled "open computing" (the idea that anyone could exercise the power of content creation or effect control over their own systems and data), but also the missing building blocks that should have been but weren't.
Instead of walled off corporate gardens like Facebook, Google, Twitter or any of the other behemoths that offer little but take much, wikis are probably some of the best examples of how the Internet should have been. Technologies like Gopher, though not entirely dead, were left in the dust in our pursuit of flash, convenience and the almighty dollar. Somewhere along the way we lost the ability to exert our will over the technology we use and sadly, our lack of interest and attention have resulted people using Facebook as a news source of all things. Read this interview with Noam Chomsky if you want to understand just how influential a "news source" can be.
The blame for the current state of the web can perhaps be laid at the feet of high school educators. I know this sounds absurd at first, so you'll have to bear with me for a minute while I explain. The high school years are crucial for young people who are beginning to develop a "world view" that moves beyond being merely passive actors on the global stage. With electronic technology the ever pervasive medium for facilitating communication, forming communities and consuming news, it is more important than ever that young people be taught how to navigate such technology and understand the consequences involved. How much more difficult would it be for tyrants, governments and CEOs to effect their plans if citizens were more enlightened and aware of how technology can be used against them, and how they can empower change by being in control of their technology. Sadly, few courses are available for young people during these formative years and even fewer are the educators who really understand what is at stake.
All is not lost, though. The first steps to asserting your control over the web can be taken by learning how to self-publish.
How does one self-publish?
You can send email. For anything more complicated than "please pick up some eggs", it's still the best way to communicate one-on-one or one-to-many.
You can create free, fast web pages through txti.es. A txti page uses Markdown to format the page. It's not difficult to use.
You can start a wiki with some free software like TiddlyWiki or WikidPad.
You can start a blog with Micro.blog or any of the other free blogging platforms.
The next steps might be Beyond the Web.
As previously mentioned, the Dell PowerEdge T710's stock Pulse Width Modulated (PWM) fans are controlled by the iDRAC6 & BMC firmware data files. I haven't had time to properly address these components but luckily there is another quick method that we can use to silence the stock fans. Later on I also tried swapping out the stock fans (YouTube video) with much quieter Arctic F9 PWM models but this introduced other problems.
Read More
I have an aging Dell T710 that I bought a number of years ago. I use it to offload long running processes, handle file sharing, shared services, jails and so on. It's been running FreeBSD for a couple of years since I moved away from Linux.
Like most server-class hardware this tower is particularly loud. Dell shipped it with pulse width modulated fans that are anything but quiet and thanks to the iDRAC6 Express software that runs on a WPCM450 integrated baseboard management controller (BMC) the fan control & throttling makes it sound like a jet is taking off. That's fine if you have somewhere to put it but we've moved to a small apartment and it has to sit in our office. As we're fans of hearing ourselves think (pun intended) I needed some way to wrestle control away from the default iDRAC firmware.
The WPCM450 runs a version of Busybox Linux on an ARM processor. As you would expect, Dell has heavily customized this software and provides access to it via a web interface, Telnet, SSH, RAC, IPMI or Serial interface to RAC/IPMI. None of these options offer the controls we're looking for and the SSH/Telnet options are locked down to the iDRAC SM-CLP command line interface. In short, Dell has turned an otherwise very useful out-of-band management tool into a glorified toaster oven.
Previous versions of the Dell BMC have been reverse engineered by others however the Dell T710 is an 11th generation server so sadly we can't use those methods.
Read More
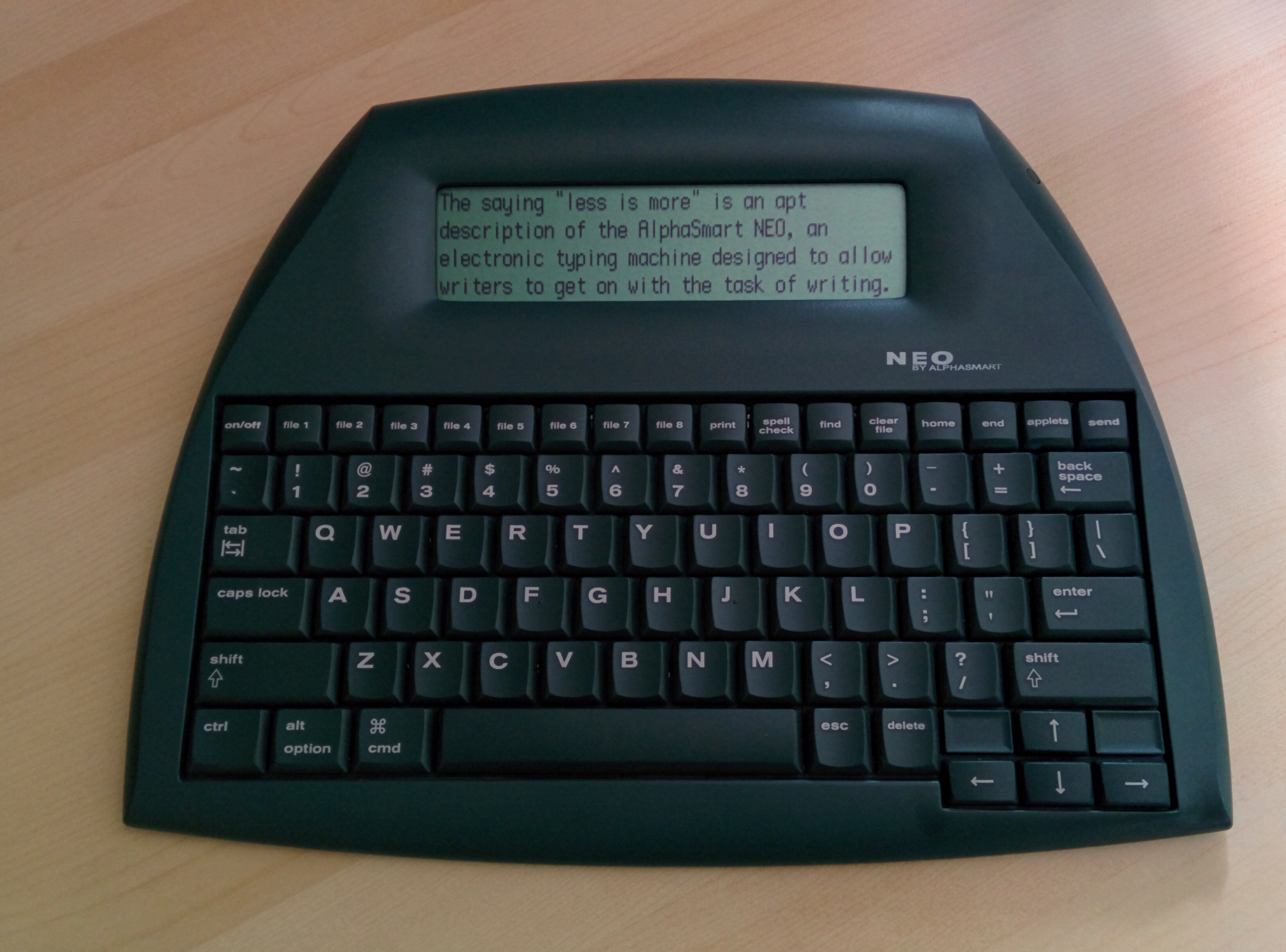
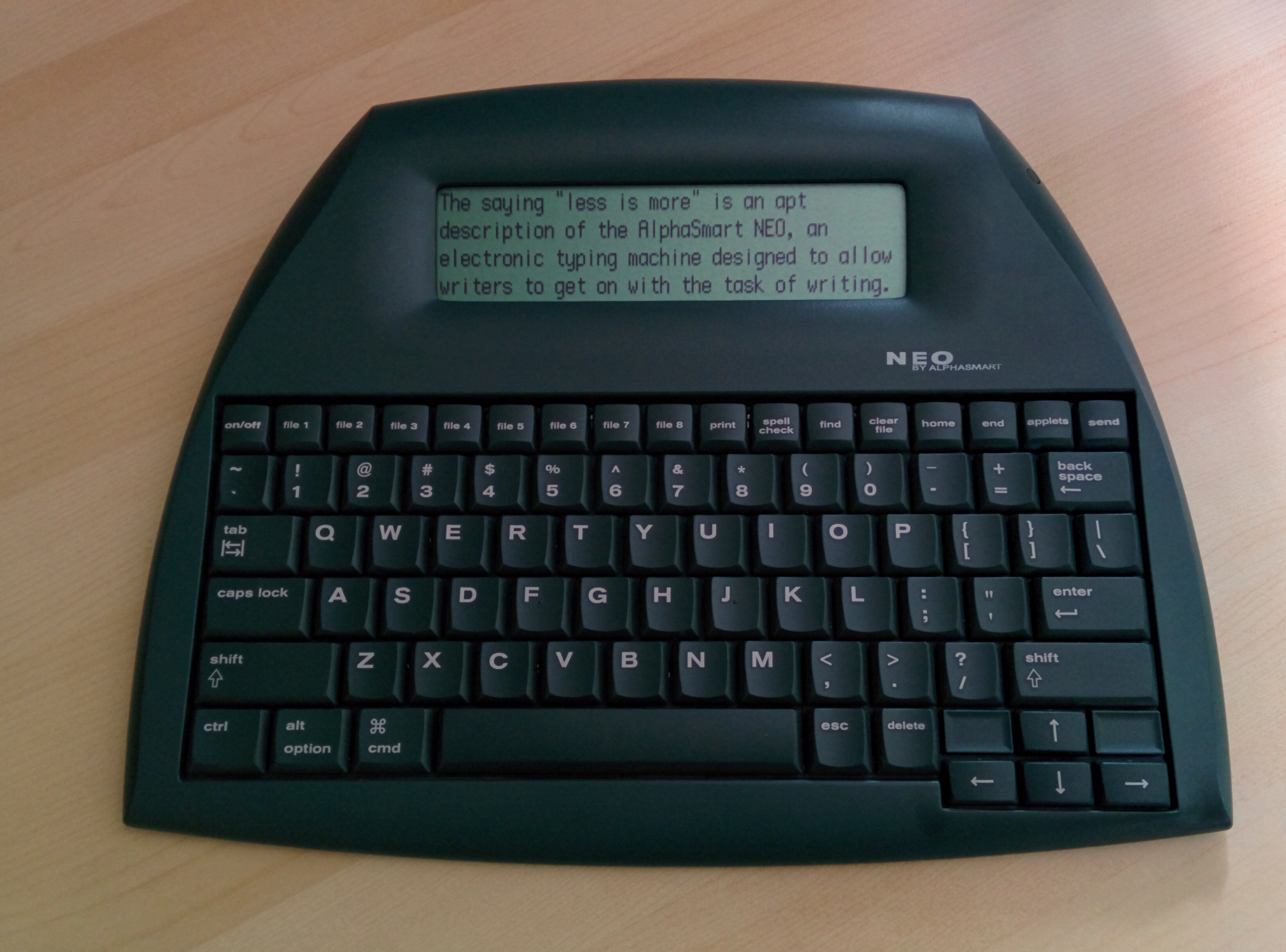
The saying "less is more" is an apt description of the AlphaSmart NEO, an electronic typing machine designed to allow writers to get on with the task of writing. It eschews all of the fancy options you'd expect to find in a word processor. In fact, with a default configuration the display is limited to four lines of 44 characters and in any case the NEO makes for a poor text editor but what it lacks in features it makes up for with an emphasis on simplicity that is surprisingly effective as a tool to channel your creative outlet.
Read More